
Choose any of the searching criteria to restore lost data. Here we are going to select 'Photo Search' mode for demonstration purpose.
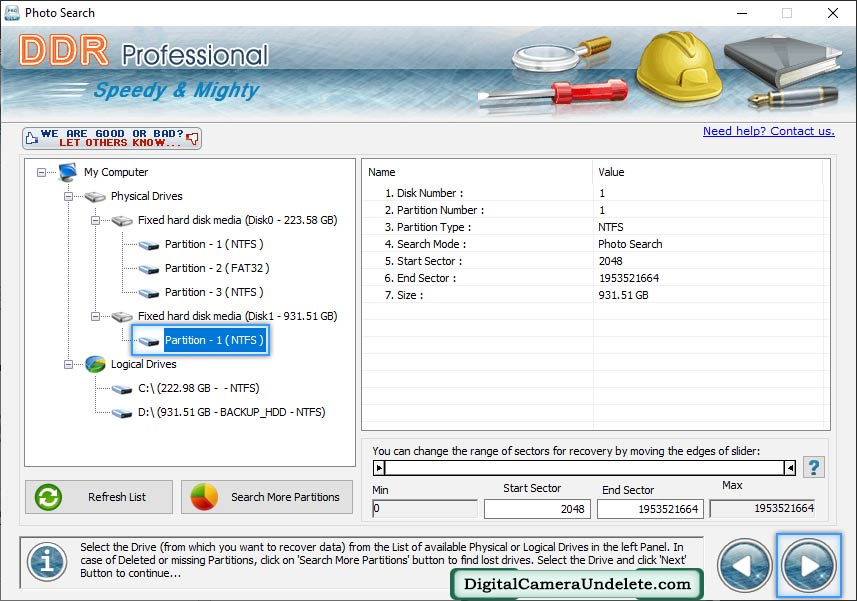
Select disk partition or drive from which you want to recover data. In case of deleted or missing partitions, click on 'Search More Partitions' button.
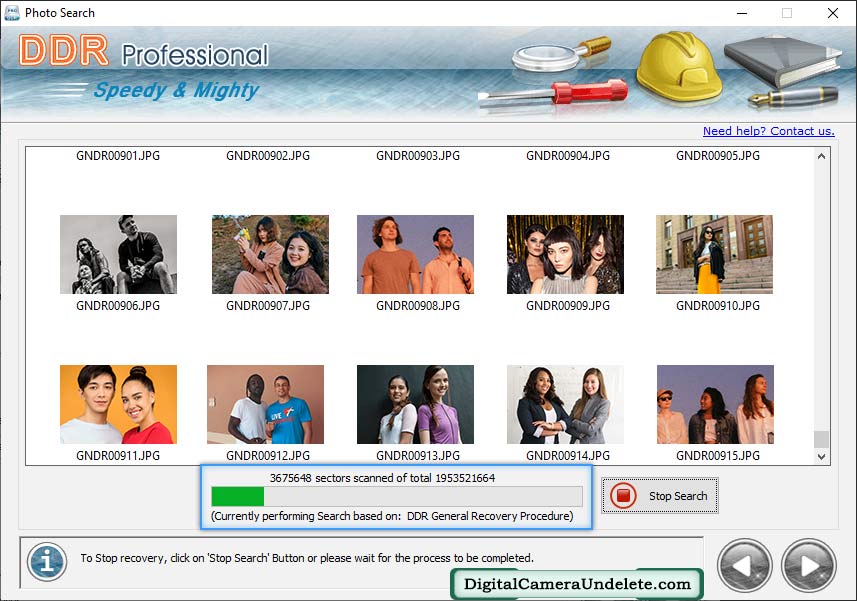
Currently performing scanning process, You can stop searching process by clicking on "Stop" button.
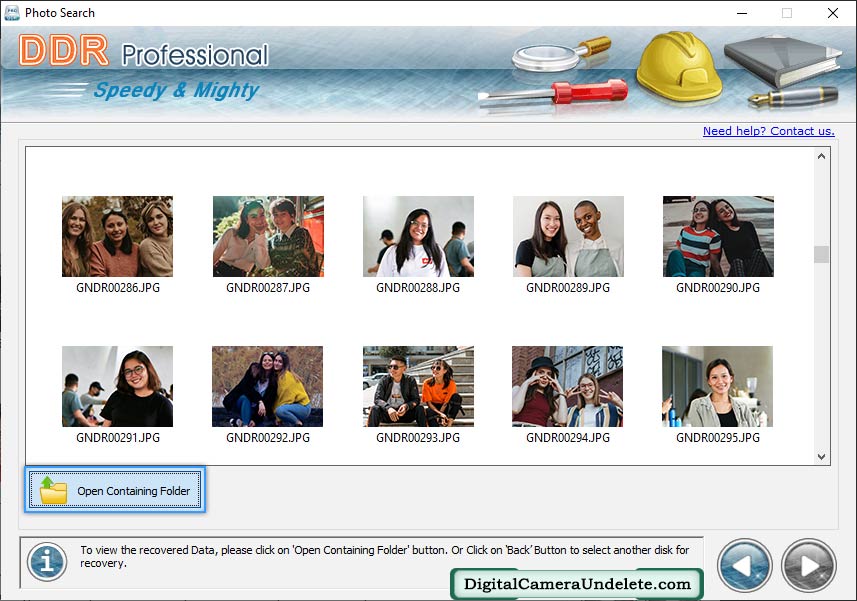
Data has been recovered successfully. To view your recovered data, click on 'Open Containing Folder' button.
The proliferation of mobile devices has led to a significant increase in the demand for International Mobile Equipment Identity (IMEI) generators. One such tool that has garnered attention in recent times is the Advanced IMEI Generator v100 Free. This paper aims to provide an in-depth analysis of the features, functionality, and implications of using this tool. We examine the capabilities of the Advanced IMEI Generator v100 Free, its potential applications, and the risks associated with its use.
The IMEI is a unique 15-digit identifier assigned to every mobile device. It serves as a crucial component in mobile network security, device tracking, and identification. However, with the increasing demand for mobile devices, some users may seek alternative methods to generate IMEIs for their devices. This is where tools like the Advanced IMEI Generator v100 Free come into play. advanced imei generator v100 free
The Advanced IMEI Generator v100 Free is a tool that warrants caution and scrutiny. While it may have legitimate applications in device repair and maintenance, its potential for misuse and implications for network security and device identity are significant concerns. As the use of IMEI generators continues to evolve, it is essential to establish clear guidelines, regulations, and best practices to ensure the secure and responsible use of these tools. The proliferation of mobile devices has led to